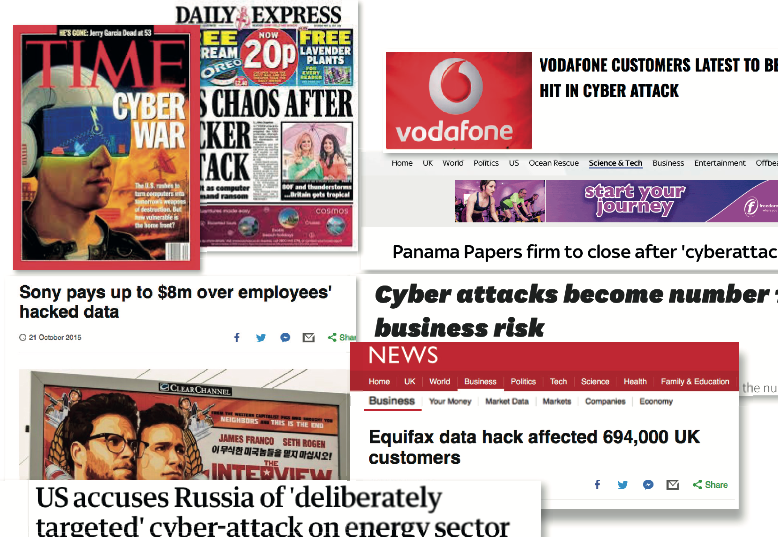
Think your business is of no interest to a cyber criminal? Think again. As security tightens up at the top, mid-sized businesses are increasingly being targeted. AVTE spoke to Kaspersky Lab, one of the world’s leading software security firms to find out more.
How big is the threat of cyber-crime for businesses today?
Business-critical processes and confidential data are being increasingly exposed to cyber threats, with one in three (38 per cent) organisations being affected by malware over the last year. It’s now no longer a question of if your business will – be hit, but when – and how much it will cost. The latest Kaspersky Lab Corporate IT Security Risks survey found that the average cost of a data breach stands at £63K for SMBs and £771K for enterprises, up around 11 per cent from last year.
Based on what we’ve seen in the press – is this more of a problem for larger organisations?
As military contractors and high-profile enterprises continue to gain awareness and bolster defences, mid-sized and small enterprise companies become the next logical step for targeted attacks.
What should they do?
Future generations must prepare themselves for waves of increasingly malicious threats perpetrated by foreign agencies, hostile governments, political hacktivists and unscrupulous companies illicitly stealing secrets.
Many mid-market attacks can be mitigated or stopped with regular user education and training. Best security practices such as avoiding clicking on attachments and PDFs from unknown or unsolicited sources, double-checking suspicious emails and regularly changing passwords should be applied frequently.
The mid-market must improve its defences to mitigate increasingly menacing threats. Standard firewalls and IDS technology are not enough to block evasive and sophisticated attacks.Complicating matters, many of these technologies are not adequately monitored or updated, lulling end-user organisations into a false sense of security, while giving a free pass to the operators. As a bare minimum, mid-market companies need to have a strong endpoint security agent that incorporates anti-virus, application control, device control and web control.
Most cyber-threats will typically rely on little-known, or unknown vulnerabilities.
What should a company do if they’re unsure how secure/protected they are?
We recommend conducting a security audit that usually includes penetration testing – a security service which shows various attack scenarios for different types of attackers.
How vulnerable is equipment used on a network?
Any smart device is a computer with an OS that controls and operates a technological process. Usually, smart devices are based on the Linux OS and have external network connections via HTTP/HTTPS (standard Web interface), FTP, Telnet or SSH. In some companies, such devices are part of an internal network with other classical computers.
In order to keep your network safe, separation is key: any devices that are using network connections should be separated from the main corporate network. Secondly, the company needs to update all software installed on all devices on a regular basis, even the smart coffee machine, and always change the default password. As for industrial control systems (ICS), it is highly recommended to use special security network monitoring solutions to prevent a potentially catastrophic event.
What is the biggest threat to security?
Against the backdrop of a complex and growing cyber-threat landscape, where 57 per cent of businesses now assume their IT security will become compromised, businesses are also waking up to the fact that one of the biggest chinks in their armour against cyber attack is their very own employees. Fifty-two per cent of businesses admit that employees are their biggest weakness in IT security, with their careless actions putting business IT security strategy at risk.







